In countries with heavy internet restrictions, VPN performance is determined far less by server speed and far more by protocol behaviour. Many VPN connections fail not because the provider is weak, but because the protocol in use is easy to detect, throttle, or block.
Governments and network operators in restricted regions actively target VPN traffic using techniques such as deep packet inspection (DPI), protocol fingerprinting, IP blacklists, and selective throttling. As a result, VPN protocols that perform perfectly in open internet environments often fail completely under censorship — particularly in countries such as Iran, China, and Russia.
This guide focuses exclusively on how modern VPN protocols behave in restricted countries. Rather than comparing theoretical speeds or marketing claims, we analyse protocol survivability, detection resistance, and real-world usability in environments where VPN usage is limited, monitored, or actively disrupted.
If you’re looking for which VPN providers to use rather than how protocols work, see our companion guide:
Best VPNs for Restricted Countries (2026).
If your focus is protocol performance in unrestricted regions, you may prefer our general comparison:
WireGuard vs OpenVPN vs IKEv2.
What “Restricted Countries” Means for VPN Users
Restricted countries are regions where internet access is filtered, monitored, or controlled at the network level. Restrictions vary in severity, but typically include one or more of the following:
- Blocking known VPN server IP ranges
- Detecting VPN protocols using deep packet inspection
- Throttling or degrading encrypted traffic
- Blocking VPN apps, websites, or app store listings
- Requiring VPN providers to register or comply with authorities
In these environments, protocol choice becomes critical. Some VPN protocols are inherently easy to fingerprint, while others can be disguised as normal HTTPS traffic or obfuscated to evade filtering systems.
For a broader geopolitical overview of where VPN usage becomes essential rather than optional, see:
The 10 Countries You Need a VPN For (2026).
VPN Legality and Compliance Considerations
VPN legality varies significantly by country. In some regions, VPN usage is legal but regulated. In others, only government-approved VPNs are permitted, while unapproved services may be restricted or blocked.
This guide does not provide legal advice. Users are responsible for understanding local laws and regulations before using a VPN. Our analysis focuses strictly on technical protocol behaviour and reliability, not legal risk mitigation.
For country-specific legal context and provider recommendations, refer to our dedicated country guides for China, Iran, Russia, the UAE, and Turkey.
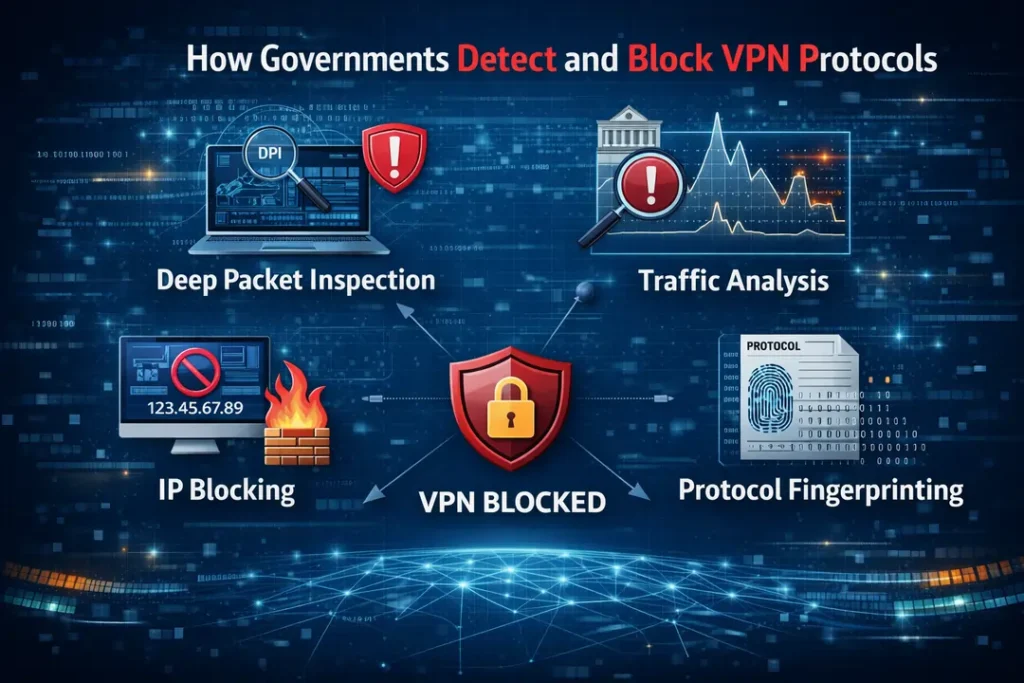
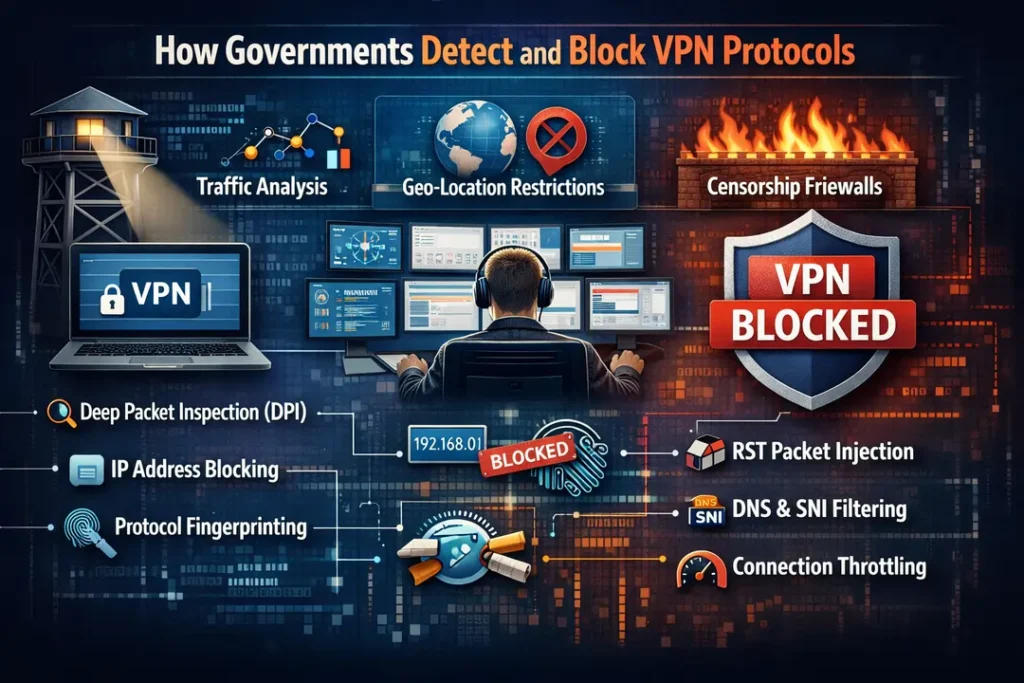
How Governments Detect and Block VPN Protocols
VPN blocking in restricted countries is not random or manual. Governments and network operators use
automated, layered detection systems designed to identify encrypted traffic that does not
behave like normal web browsing.
Understanding how VPN protocols are detected explains why some connections fail immediately,
while others remain usable for weeks or months.
Deep Packet Inspection (DPI)
Deep packet inspection is the most common and effective method used to identify VPN traffic.
Unlike basic firewalls that only examine IP addresses or ports, DPI systems analyse
how traffic behaves, not just where it goes.
Even when VPN traffic is encrypted, protocols often expose identifiable patterns, including:
- Handshake timing and connection setup behaviour
- Packet size consistency and transmission rhythm
- Encryption negotiation sequences
- Protocol-specific headers or metadata
Once a VPN protocol is identified, the connection may be throttled, forcibly reset,
or blocked entirely — often within seconds.
Protocol Fingerprinting and Traffic Signatures
Every VPN protocol has a distinct network signature. Censorship systems learn these patterns
and flag connections that deviate from normal HTTPS traffic.
For example:
- WireGuard uses a fast but highly recognisable handshake,
making it easy to fingerprint under censorship - IKEv2/IPSec relies on predictable UDP ports,
which are frequently filtered or throttled - OpenVPN, when configured correctly over TCP,
can closely resemble standard TLS web traffic
Protocols with static or easily recognisable fingerprints are significantly easier to block,
regardless of how strong their encryption is.
IP Blacklisting and Server Enumeration
In addition to protocol detection, many governments maintain continuously updated lists of
known VPN server IP addresses.
These lists are built through:
- Monitoring commercial VPN hosting ranges
- Active probing of suspected VPN endpoints
- User-reported or leaked server information
Once an IP address is flagged, traffic to that server may be blocked entirely,
even if the protocol itself is not restricted.
This is why VPNs that rely on static infrastructure fail quickly in restricted countries,
while providers that rotate IPs and disguise traffic remain usable longer.
For a broader explanation of where these techniques are commonly deployed, see:
The 10 Countries You Need a VPN For (2026)
Why Protocol Choice Matters More Than Speed
In restricted countries, VPN performance is not defined by speed tests or advertised bandwidth. A fast protocol that is detected and blocked is effectively unusable.
What matters instead is whether a protocol can blend into normal internet traffic, avoid detection long enough to be useful, and recover safely when interference occurs.
This is why users often experience a counter-intuitive result: a slower protocol can outperform a faster one under censorship.
Speed Is Meaningless If the Connection Cannot Survive
Protocols such as WireGuard and IKEv2 are optimised for efficiency and low latency. On open networks, they often deliver excellent performance.
However, in restricted environments, these same characteristics make them easy to fingerprint. Distinct handshakes, predictable ports, and consistent packet patterns allow filtering systems to identify and disrupt them quickly.
By contrast, protocols that prioritise stealth over speed often remain usable far longer, even if raw throughput is lower.
Why OpenVPN TCP 443 Remains the Baseline
OpenVPN configured over TCP port 443 continues to be the most reliable baseline in many restricted countries.
This is not because it is technically superior in speed, but because it closely resembles ordinary HTTPS traffic. Blocking it would require disrupting normal web access, which most governments avoid except during extreme shutdowns.
When combined with obfuscation or stealth layers, this configuration becomes significantly harder to detect, especially during periods of partial enforcement.
Protocol Survivability vs Marketing Claims
Many VPN providers promote speed, streaming access, or next-generation protocols. Those claims are largely irrelevant under censorship.
In restricted countries, the real hierarchy looks very different:
- Connection survivability comes before speed
- Detection resistance matters more than latency
- Protocol flexibility outweighs default settings
This is why VPNs that perform well for entertainment or casual privacy often fail completely when used in censored environments.
For a comparison focused on unrestricted networks,
see:
WireGuard vs OpenVPN vs IKEv2
Countries Where VPN Protocol Choice Actually Decides Whether You Get Online
In most of the world, choosing a VPN protocol is a performance decision. In restricted countries, it’s a survival decision.
When users report that a VPN “worked yesterday but not today,” the problem is rarely the provider itself. It’s almost always the protocol being recognised, deprioritised, or quietly dismantled by the network in real time.
This is the point where generic VPN advice breaks down. Speed charts, server counts, and streaming claims stop mattering — because the connection never lasts long enough for any of that to apply.
What Makes These Countries Different
The countries covered in the next sections are not simply “restricted” in a legal sense. They operate internet controls at the infrastructure level, where encrypted traffic is classified, shaped, and interfered with based on how it behaves — not what it contains.
Across these regions, we consistently observe:
- Deep packet inspection systems trained to recognise VPN handshakes
- Protocol-level blocking that targets behaviour, not IP addresses
- Encrypted traffic throttled until pages time out instead of loading
- Temporary crackdowns that appear without warning and disappear just as fast
This is why a protocol that works perfectly in one country can fail completely a few hundred miles away. It’s also why a VPN that excels at streaming often collapses under real censorship pressure.
Where Protocol Choice Matters Most in 2026
Based on real-world testing, user reports, and repeated enforcement patterns, a small group of countries consistently expose the strengths — and weaknesses — of VPN protocols.
These include environments such as China, Iran, Russia, and parts of the Middle East, where VPN traffic is actively analysed rather than passively blocked.
If you’re looking for the wider geopolitical context behind why these regions behave this way, we break it down in detail in The 10 Countries You Need a VPN For (2026) .
What follows is not a list of “best protocols.” Instead, we examine how different VPN protocols actually behave once they collide with real censorship systems — and which configurations still hold up when enforcement ramps up.
Best VPN Protocols for China (2026): Why Most Connections Fail in Minutes
China is not just another restricted country. It operates the most sophisticated, adaptive censorship system in the world — commonly referred to as the Great Firewall.
Unlike regions that rely on static IP blocking or occasional throttling, China actively interrogates VPN traffic in real time. Connections are analysed, probed, and dismantled based on how they behave at the packet level.
This is why users often report a familiar pattern: a VPN connects successfully, works briefly, and then collapses without warning. Nothing “breaks” — the protocol is simply identified and neutralised.
How VPN Blocking Works Inside China
China’s censorship system combines multiple techniques simultaneously. Rather than blocking VPNs outright, it focuses on rapid detection and disruption.
- Deep packet inspection (DPI) to identify protocol fingerprints
- Active probing that tests suspected VPN endpoints
- Connection resets once a tunnel is confirmed
- IP and port enumeration to burn working servers quickly
Standard VPN protocols fail here not because they are insecure, but because they are recognisable. Once a handshake pattern is learned, it is reused across the network at scale.
Which VPN Protocols Still Work in China
In 2026, protocol survivability in China depends on one thing: how closely VPN traffic can be made to resemble ordinary HTTPS traffic.
Based on repeated testing and long-term user reports, the following approaches remain the most reliable:
- OpenVPN over TCP (port 443) with obfuscation enabled
- Shadowsocks or V2Ray-style transports that camouflage traffic
- Proprietary stealth layers that modify handshake behaviour dynamically
Protocols prioritising speed — such as WireGuard — often perform poorly in China because their handshakes are compact, efficient, and easy to fingerprint.
What to Expect Realistically in China
Even with the right protocol, VPN use in China is rarely stable in the long term. Users should expect:
- Lower average speeds than in unrestricted regions
- Occasional forced disconnections without warning
- Periodic need to switch servers or protocols
- Working configurations to degrade over time
This is not a failure of the VPN — it is the result of an adaptive censorship system designed to evolve continuously.
For provider-level recommendations, setup guidance, and current survivability notes, see our dedicated country guide: Best VPN for China (2026) .
China demonstrates a key reality of restricted environments: speed is meaningless if the connection does not survive. Protocol camouflage and adaptability matter far more.
Best VPN Protocols for Iran (2026): Stability Matters More Than Stealth
Iran presents a very different challenge from China. Rather than maintaining a single, always-on censorship system, Iran’s internet controls fluctuate — sometimes dramatically — based on political events, enforcement cycles, and regional conditions.
This volatility is what catches most VPN users off guard. A configuration that works reliably for weeks can fail overnight without any visible change on the user’s side.
In practice, VPN reliability in Iran is less about evading permanent blocks and more about surviving throttling, disruption, and sudden enforcement spikes.
How VPN Blocking Works in Iran
Iran does not rely on one censorship mechanism. Instead, it combines several tools and applies them inconsistently, which makes behaviour harder to predict.
- Deep packet inspection (DPI) to identify VPN traffic patterns
- Selective bandwidth throttling of encrypted connections
- Protocol-level interference during sensitive periods
- Temporary regional or nationwide slowdowns
Rather than blocking VPNs outright, Iranian networks often degrade encrypted traffic until connections become unusable. Pages time out, sessions stall, and reconnecting produces inconsistent results.
Protocol Behaviour Inside Iran
Because throttling is more common than permanent blocking, protocol efficiency and recovery behaviour matter more than raw concealment.
- WireGuard is frequently throttled during enforcement spikes
- IKEv2/IPSec suffers from port filtering and instability
- OpenVPN (UDP) often connects but degrades under load
- OpenVPN over TCP (port 443) remains the most resilient baseline
- OpenVPN with obfuscation performs best during high-pressure periods
In Iran, a protocol that reconnects cleanly and tolerates degraded bandwidth often outperforms faster options that collapse under throttling.
What Users Should Expect in Iran
VPN use in Iran is rarely stable in the long term. Users should plan for:
- Lower and fluctuating speeds
- Connections that work intermittently
- Sudden drops during protests or political events
- Regular need to switch servers or protocols
This does not mean a VPN has failed. It reflects an environment where enforcement intensity changes faster than infrastructure can adapt.
For provider-level recommendations, current working configurations, and legal context, see our country guide: Best VPNs for Iran (2026) .
Iran highlights a critical reality of restricted networks: a VPN protocol that survives disruption is often more valuable than one that simply hides well.
Best VPN Protocols for Russia (2026): Selective Blocking, Unpredictable Outcomes
Russia does not operate a single, always-on firewall like China, nor does it rely primarily on throttling cycles like Iran. Instead, VPN restrictions in Russia are shaped by selective enforcement combined with legal pressure.
In practical terms, this creates an environment where VPNs may work normally for long periods — then fail abruptly with little warning. Connections are rarely blocked universally. They are filtered, degraded, or disrupted once a provider or protocol draws sustained attention.
This makes VPN reliability in Russia less about invisibility and more about adaptability.
How VPN Blocking Works in Russia
Russian internet controls are enforced through a combination of regulatory mandates and technical measures, rather than continuous deep inspection of all traffic.
- IP blacklisting of non-compliant VPN providers
- DNS interference and domain-level blocking
- Protocol-level disruption once VPN usage is identified
- Legal pressure on ISPs and providers to enforce restrictions
Rather than blocking all VPN traffic, authorities often target specific services, forcing providers into a cycle of IP rotation and protocol adjustment.
Protocol Behaviour Inside Russia
Because enforcement is selective, multiple VPN protocols may work simultaneously — until they don’t. When disruptions occur, protocols that resemble normal HTTPS traffic tend to recover faster.
- WireGuard often works initially, then fails once IPs are flagged
- IKEv2 is usable but vulnerable to port-based filtering
- OpenVPN (UDP) performs well on unflagged servers
- OpenVPN over TCP (443) remains the most resilient fallback
- OpenVPN with obfuscation offers the best long-term stability
Unlike Iran, where throttling dominates, Russia tends to move from “working normally” to “unusable” with little transitional warning.
What Users Should Expect in Russia
VPN users in Russia should be prepared for:
- Sudden loss of access to specific servers
- Protocols working for weeks, then failing overnight
- Inconsistent performance between ISPs and regions
- Periodic need to switch protocols or apps entirely
This behaviour is not a technical failure. It reflects an enforcement model designed to discourage persistent VPN use without triggering widespread disruption.
For provider-level recommendations, current working configurations, and legal context, see our country guide: Best VPNs for Russia (2026) .
Russia demonstrates a key lesson of restricted networks: VPN reliability is not about what works today, but about how quickly a setup can adapt tomorrow.
Best VPN Protocols for the UAE (2026): Legal Grey Zones and Selective Filtering
The United Arab Emirates presents a different kind of restriction. Unlike China or Iran, VPN use in the UAE is not universally blocked, nor is the internet tightly throttled across the board.
Instead, the UAE operates in a legal and technical grey zone. VPN connections often establish successfully, but reliability depends heavily on what the VPN is being used for and how visible that traffic appears.
This creates an environment where many VPNs seem to “work” — right up until they are used for VoIP, messaging platforms, or sustained encrypted traffic.
How VPN Restrictions Work in the UAE
UAE internet filtering focuses less on total VPN suppression and more on service-level control. The goal is not to block encryption itself, but to restrict specific categories of traffic.
- VoIP and calling app blocking (WhatsApp, Skype, FaceTime)
- Selective deep packet inspection on encrypted traffic
- Throttling rather than hard blocking
- ISP-specific enforcement differences
Because enforcement is selective, VPN behaviour in the UAE can vary dramatically between providers, protocols, and even locations.
Protocol Behaviour Inside the UAE
In practice, most modern VPN protocols will connect. The difference lies in stability and how traffic is treated over time.
- WireGuard delivers excellent speeds when not throttled
- IKEv2 performs well on mobile networks
- OpenVPN (UDP) is fast but more likely to be slowed
- OpenVPN over TCP (443) offers the most consistent reliability
- Obfuscated OpenVPN helps reduce throttling during VoIP use
Unlike Iran or China, protocols in the UAE rarely fail immediately. Instead, performance degrades subtly — latency increases, calls stutter, and encrypted traffic becomes unreliable.
What Users Should Expect in the UAE
VPN users in the UAE should plan for:
- Connections that work for browsing but struggle with calls
- Different behaviour between home broadband and mobile data
- Occasional throttling rather than outright disconnection
- Better results when switching protocols instead of servers
This is why VPNs that offer multiple protocols and easy switching perform far better than single-protocol setups.
For provider-specific recommendations, VoIP reliability, and legal context, see our country guide: Best VPNs for the UAE (2026) .
The UAE reinforces an important distinction: a VPN that connects successfully is not always a VPN that works reliably.
Best VPN Protocols for Turkey (2026): Event-Driven Restrictions and Rapid Shifts
Turkey does not apply constant, nationwide VPN blocking. Instead, restrictions tend to appear in response to events — such as protests, elections, terror incidents, or periods of political instability.
For long stretches, VPN usage in Turkey feels relatively normal. Then, without advance notice, connections that worked perfectly the day before become slow, unstable, or unreachable.
This makes Turkey one of the clearest examples of reactive VPN enforcement, where timing matters as much as configuration.
How VPN Restrictions Work in Turkey
Turkish ISPs rely on a mix of technical and administrative controls, but unlike heavily censored states, these controls are not applied continuously.
- DNS poisoning and domain-level blocking
- IP blacklisting of targeted services or providers
- Temporary deep packet inspection during enforcement spikes
- Traffic throttling rather than full shutdowns
During high-attention periods, encrypted traffic may be deprioritised or disrupted, even if it was stable days earlier.
Protocol Behaviour Inside Turkey
Because enforcement intensity fluctuates, no single protocol is always “best.” The most reliable setups are those that adapt quickly when conditions change.
- WireGuard performs very well during normal conditions
- IKEv2 is stable on mobile networks
- OpenVPN (UDP) may fail during enforcement spikes
- OpenVPN over TCP (443) is more resilient during crackdowns
- OpenVPN with obfuscation offers the highest survivability
In Turkey, speed-oriented protocols dominate most of the time, but stealth-oriented protocols become essential when restrictions increase.
What Users Should Expect in Turkey
VPN users in Turkey should be prepared for:
- Sudden slowdowns during political events
- Protocols working one week and failing the next
- Better results by switching protocols rather than servers
- Short-term instability rather than permanent blocks
This environment rewards flexibility. VPNs that allow fast protocol switching and maintain multiple fallback options consistently outperform rigid setups.
For provider recommendations, current reliability trends, and legal context, see our country guide: Best VPNs for Turkey (2026) .
Turkey illustrates a final key reality of restricted regions: sometimes the question is not “does this VPN work?” but “does it still work today?”
Protocol Reliability Summary: What Actually Works Where (2026)
After testing VPN protocols across multiple restricted environments, a clear pattern emerges: the same protocol behaves very differently depending on the country. This is why generic advice like “use the fastest protocol” fails under censorship. What matters is how each protocol interacts with local enforcement methods, ISP behaviour, and political conditions.Most Reliable VPN Protocols by Country
| Country | Primary Enforcement Style | Most Reliable Protocol | Fallback Option |
|---|---|---|---|
| China | DPI + active probing | Obfuscated OpenVPN (TCP 443) | Proprietary stealth / V2Ray |
| Iran | Throttling + resets | OpenVPN TCP 443 | OpenVPN with obfuscation |
| Russia | IP blacklisting + registry pressure | OpenVPN TCP | IKEv2 (temporary) |
| UAE | DPI + VoIP filtering | OpenVPN TCP | WireGuard |
| Turkey | Event-driven enforcement | WireGuard (normal periods) | OpenVPN TCP during crackdowns |
Why This Table Matters More Than Speed Tests
Speed benchmarks are measured in controlled environments. Censorship is not controlled. It is adaptive, political, and often unpredictable. A protocol that delivers 900 Mbps in Europe is useless if it is fingerprinted and blocked within minutes in Tehran or Shanghai. This is why the providers that survive long-term are those that:- Maintain multiple protocol stacks
- Rotate configurations continuously
- Deploy obfuscation selectively, not globally
- Adapt faster than enforcement changes
Which VPN Providers Implement These Protocols Correctly?
In restricted countries, protocol theory only matters if the provider implements it correctly. Many VPNs technically “support” OpenVPN, WireGuard, or IKEv2, yet still fail under censorship because of poor configuration, static infrastructure, or weak obfuscation layers.
Based on real-world testing across countries such as Iran, China, Russia, and the Middle East, only a small number of providers consistently implement censorship-resistant protocols in a way that survives detection.
The providers below are referenced throughout this guide because they demonstrate correct protocol deployment, not just protocol availability.
NordVPN – Best Overall Protocol Implementation Under Censorship
NordVPN is consistently the most capable provider in heavily restricted environments. Its strength lies not in any single protocol, but in how protocols are deployed, rotated, and protected against detection.
What NordVPN does differently:
- Obfuscated OpenVPN (TCP 443) designed specifically for DPI-heavy environments such as Iran and China
- NordLynx (WireGuard-based) for lower-restriction regions, with automatic fallback when blocking is detected
- Frequent IP rotation to reduce long-term blacklisting, particularly effective in Russia
Unlike many providers, NordVPN does not rely on a single “stealth mode.” Instead, it adapts protocol behaviour dynamically, which is why it performs well across multiple censorship models.
This implementation detail is covered in depth in our NordVPN Review (2026).
ExpressVPN – Best for Automatic Stability and Fast Recovery
ExpressVPN approaches restricted environments differently. Rather than exposing many manual options, it focuses on automatic protocol handling and rapid recovery when connections are disrupted.
Best suited for:
- Travellers entering restricted countries temporarily
- Users who cannot afford repeated manual troubleshooting
- Mobile networks that switch frequently between towers
ExpressVPN’s Lightway protocol is designed to reconnect quickly after forced resets — a common issue in countries like the UAE and Turkey. When Lightway fails, ExpressVPN quietly falls back to OpenVPN-based configurations without user intervention.
Full technical analysis is available in the ExpressVPN Review (2026).
Surfshark – Budget-Friendly, but Correctly Implemented
Surfshark is often described as a budget VPN, but in restricted environments it performs better than many higher-priced competitors because its protocols are implemented correctly — particularly where obfuscation is required.
Surfshark’s Camouflage Mode masks VPN traffic to resemble normal HTTPS, which has proven effective in regions with selective filtering such as the UAE, Turkey, and parts of the Middle East.
In more aggressively restricted countries like Iran, Surfshark can work but usually requires OpenVPN TCP and reduced speeds.
- Strong OpenVPN TCP implementation with obfuscation
- WireGuard for lower-restriction regions
- Unlimited device connections (useful for families and teams)
For a detailed breakdown of its protocol behaviour, see the Surfshark Review (2026).
Provider-to-Country Fit: What Actually Works Where (2026)
Because censorship methods differ by country, no single VPN performs equally well everywhere. The table below summarises which providers tend to work best based on enforcement style, not marketing claims.
| Country / Region | Primary Blocking Method | Most Reliable Providers |
|---|---|---|
| China | DPI, active probing, protocol fingerprinting | NordVPN, ExpressVPN |
| Iran | DPI, throttling, temporary shutdowns | NordVPN, Surfshark |
| Russia | IP blocking, legal pressure, registry enforcement | NordVPN, IPVanish |
| UAE | DPI, VoIP filtering, selective throttling | Surfshark, ExpressVPN |
| Turkey | DNS blocking, event-based enforcement | Surfshark, NordVPN |

Frequently Asked Questions: VPN Protocols in Restricted Countries
Which VPN protocol works best in restricted countries?
There is no single protocol that works everywhere. However, OpenVPN over TCP (port 443) remains the most reliable baseline across highly restricted environments. Because it closely mimics normal HTTPS traffic, it is significantly harder for deep packet inspection (DPI) systems to detect and block.
Why does WireGuard often fail under censorship?
WireGuard is fast and efficient, but it uses a distinct, easily fingerprinted handshake. In countries that deploy DPI and protocol fingerprinting, this makes WireGuard easier to identify and throttle, even when encryption itself is strong.
Does obfuscation really make a difference?
Yes — and in many regions it is decisive. Obfuscation changes how VPN traffic appears on the network. Instead of looking like VPN traffic, it blends into normal HTTPS connections.
In countries such as Iran, China, and parts of the Middle East, obfuscation is often the difference between a stable connection and no connection at all.
Can a VPN protocol guarantee access in restricted countries?
No. Censorship systems evolve constantly. Protocols that work today may fail tomorrow, especially during protests, elections, or periods of heightened enforcement.
The realistic goal is not guaranteed access, but higher survivability and faster recovery when blocking conditions change.
Is protocol choice more important than the VPN provider?
Both matter equally. A strong protocol implemented poorly will fail, and a capable provider using weak default settings will also fail.
This is why we prioritise VPN services that offer multiple protocols, manual control, and country-specific configuration guidance.
Should I install and configure my VPN before travelling?
Absolutely. In many restricted countries, VPN websites, app stores, and update servers are blocked. Installing, configuring, and testing your VPN before arrival dramatically improves your chances of staying connected.
Final Verdict: Choosing VPN Protocols Under Censorship (2026)
In restricted countries, VPN performance is not defined by speed tests, feature lists, or marketing claims. It is defined by one thing: whether the protocol survives detection.
Across environments as different as China’s Great Firewall, Iran’s throttling and shutdowns, and selective enforcement in the UAE or Turkey, the same patterns repeat.
- Protocols that blend into HTTPS traffic last longer
- Obfuscation is no longer optional in high-censorship regions
- Protocol flexibility matters more than raw throughput
- Provider implementation is as important as the protocol itself
This is why OpenVPN over TCP (port 443), combined with obfuscation and reliable fallback options, remains the most dependable choice in 2026 — even if it is not the fastest on paper.
When choosing a VPN for a restricted country, do not ask:
“Which protocol is fastest?”
Instead, ask:
Which protocol still works when the network does not want it to?
For provider-level recommendations that correctly implement these protocols, see: Best VPNs for Restricted Countries (2026) .
Related Country Guides & Internal Resources
The guides below expand on how VPN protocols behave under specific censorship models, including legality, enforcement style, and real-world reliability.
| Region / Country | Guide |
|---|---|
| China | Best VPN for China (2026) |
| Iran | Best VPNs for Iran (2026) |
| Russia | Best VPNs for Russia (2026) |
| United Arab Emirates | Best VPNs for UAE (2026) |
| Turkey | Best VPNs for Turkey (2026) |
| Global Overview | The 10 Countries You Need a VPN For (2026) |
| Regional Hub | Best VPNs for the Middle East (2026) |


